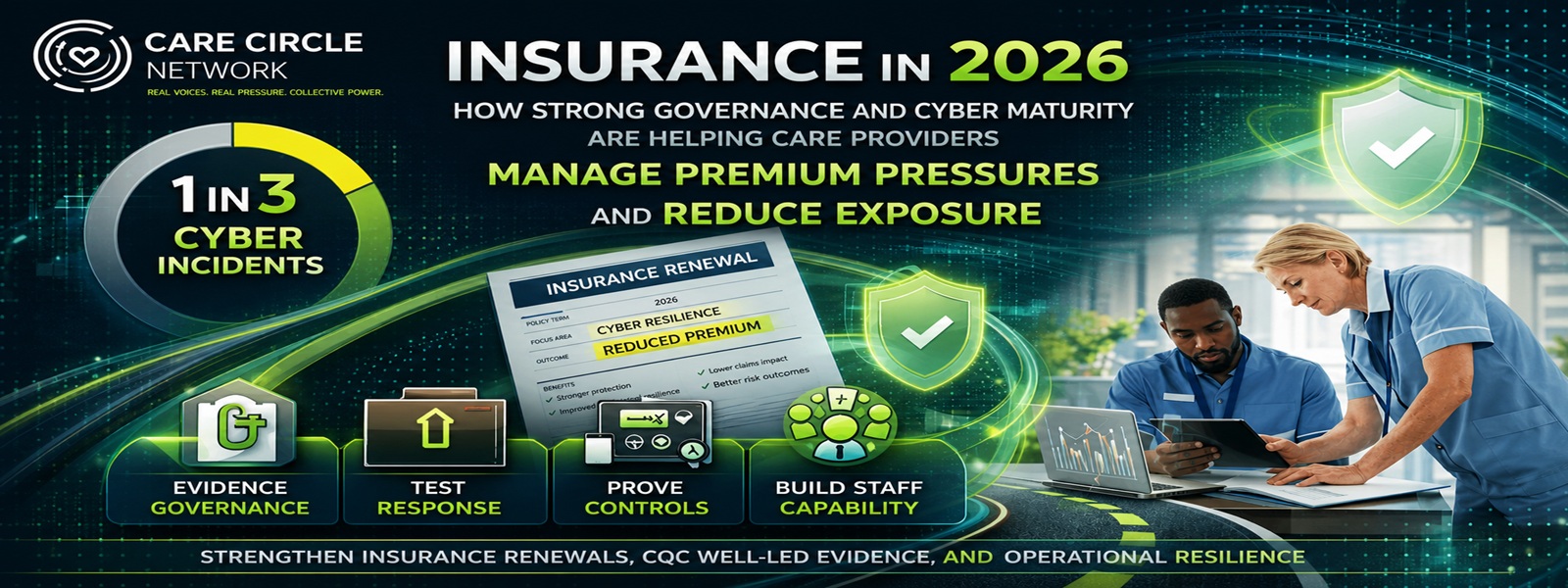
Cyber incidents continue to disrupt care delivery, with around one in three providers reporting experiences in recent years, and phishing remains the dominant threat. In response, insurers are placing greater weight on governance, controls, and technical maturity at renewal.
Here’s how forward-thinking providers are strengthening their position in a tougher market — while also building stronger operational resilience and better CQC evidence.
Cyber risk has become one of the most pressing operational and financial challenges facing adult social care providers in 2026.
With the rapid expansion of technology-enabled care (TEC), the continuing digital telecare migration, and tighter margins following the NLW rise, even a short period of system downtime or a data breach can have immediate consequences. Missed visits, locked rostering systems, disrupted digital records, emergency agency costs, GDPR exposure, and increased scrutiny under the Safe and Well-led domains are no longer theoretical risks. They are practical operational realities.
Recent data underlines the scale of the challenge. The government’s Cyber Security Breaches Survey 2025 found that 41% of health and social care organisations experienced a breach or attack in the previous 12 months, with phishing accounting for the vast majority. A separate review focused on adult social care found that around one in three providers had experienced a cyber incident within the last three years, although actual exposure may be higher given inconsistent monitoring and reporting across the sector.
The insurance market is responding accordingly.
Renewals are becoming more detailed. Underwriters are looking more closely at governance, incident response, technical controls, supplier dependencies, and how cyber risk is overseen at leadership level.
The real divide in 2026 is no longer between providers who have cyber risk and those who do not.
It is between providers who can clearly evidence cyber governance at renewal — and those who cannot.
The good news is that providers treating cyber resilience as part of mainstream governance are putting themselves in a stronger position. While outcomes always depend on an organisation’s specific profile and insurer appetite, providers with demonstrable maturity are typically seeing more constructive renewal discussions, clearer policy terms, stronger internal assurance, and reduced exposure to avoidable disruption.
Why This Matters Right Now
This issue matters now because cyber risk is no longer sitting in the background. It now overlaps directly with care quality, operational resilience, leadership oversight, and financial control.
1. Direct care impact
Ransomware, phishing, or system failure can affect rostering, telecare, medication records, communication systems, and care planning platforms. In care settings, that is not just a digital issue — it is a people issue.
2. Cost amplification
In a sector already managing NLW increases, training pressures, and energy volatility, cyber-related disruption can quickly escalate into high cost through downtime, cover arrangements, recovery work, and reputational harm.
3. Regulatory overlap
Under the evolving CQC Adult Social Care Assessment Framework 2026, visible leadership oversight of digital systems, risk, and data security increasingly strengthens Well-led evidence and supports broader governance narratives.
4. Insurance market reality
Insurers are differentiating more clearly between providers with basic controls and those with a more mature, well-evidenced approach. Organisations without clear documentation, tested plans, or leadership oversight risk higher premiums, larger excesses, restricted terms, or reduced choice at renewal.
This is why cyber maturity is no longer simply a technical aspiration. It is becoming a practical commercial and governance issue.
What Forward-Thinking Providers Are Doing Differently
The strongest providers are not treating cyber as a standalone IT matter. They are embedding it into existing governance systems so that renewal, compliance, and operational resilience reinforce each other.
The following areas are emerging as the most important.
| Area of Focus | Why It Matters | Practical Benefit |
| Board-level oversight and reporting | Demonstrates accountability and active governance | Stronger Well-led evidence and more constructive renewal conversations |
| Documented controls such as MFA, patching, backups, and segmentation | Stronger, well-led evidence and more constructive renewal conversations | Lower disruption risk and stronger insurer confidence |
| Tested incident response and business continuity plans | Shows ability to recover and continue safely | Reduced exposure to prolonged downtime and operational loss |
| Staff awareness and phishing resilience | Phishing remains the dominant attack route | Better workforce capability and fewer avoidable incidents |
| Third-party supplier and platform review | Digital care increasingly depends on external systems | Stronger supply-chain assurance and improved risk posture |
These are not perfection measures. They are practical maturity signals.
And that matters, because in the current market, insurers are increasingly looking for evidence that cyber resilience is not just written down, but actively managed.
From Renewal Pressure to Leadership Opportunity
This is where the most proactive providers are changing the conversation.
Rather than approaching renewal as a last-minute insurance exercise, they are using it as a governance review point.
That means asking:
- Can we clearly show what our current controls are?
- Are our incident and continuity plans tested, not just documented?
- Do senior leaders see cyber risk in a structured, regular way?
- Are staff being trained in a way that improves confidence and reduces avoidable error?
- Do we understand where our third-party dependencies sit?
This shift matters because it turns cyber from a defensive cost into a leadership asset.
Done well, the same work that supports stronger renewal conversations also strengthens:
- internal assurance
- operational continuity
- CQC evidence
- workforce confidence
- decision-making at board level
That is exactly the kind of dual-value approach providers need in 2026.
A Practical Four-Step Renewal Readiness Approach
For providers looking to strengthen their position now, the most effective route is usually a simple staged approach.
1. Get the governance basics visible
Make sure cyber appears regularly on the board or senior leadership agenda. Use a concise reporting format covering current risks, control status, incidents, third-party issues, and progress actions.
If leadership cannot see it clearly, neither can insurers or inspectors.
2. Confirm your core controls are real and current
Review whether key protections are fully in place and evidenced:
- Multi-factor authentication
- Patch management
- Secure, tested backups
- Access controls
- Device and network segmentation where appropriate
The goal is not technical perfection. The goal is confidence that the basics are genuine, current, and usable.
3. Test response, not just documentation
A plan that has never been tested offers limited reassurance.
Run simple response exercises:
- What happens if rostering is unavailable?
- What happens if staff cannot access care records?
- How would visits continue if a key system failed?
- Who makes decisions and how quickly?
These are exactly the questions that expose whether resilience is operational or theoretical.
4. Build staff capability, not just awareness
Cyber remains heavily people-dependent. Staff need more than a policy acknowledgement.
Short, regular, practical awareness activity around phishing, password hygiene, unusual requests, and escalation routes is far more valuable than a one-off annual exercise. This is also where cyber resilience becomes a workforce capability issue, not just a technical one.
Why This Also Supports CQC
One of the strongest aspects of this work is that it does not sit in isolation.
When cyber governance is embedded properly, it supports several things inspectors increasingly look for:
- leadership visibility
- risk identification and response
- continuity planning
- learning culture
- oversight of digital systems
- evidence that governance leads to real-world protection
That is especially relevant in Well-led, but also strengthens narratives under Safe where digital disruption could affect continuity and protection from harm.
In other words, better cyber maturity does not just improve insurer confidence. It helps demonstrate that the service is governed in a way that is active, responsive, and outcome-focused.
Turning Pressure into Resilience
The insurance environment for adult social care is not getting simpler.
But this is one area where stronger leadership can create a genuine advantage.
Providers who embed cyber maturity into governance are doing more than improving their insurance position. They are reducing avoidable disruption, strengthening operational resilience, protecting the people they support, and building better evidence for CQC.
That is why the smartest providers are no longer asking whether cyber belongs in the leadership conversation.
They are treating it as a core part of how a safe, well-led, and financially resilient service is run.
Final Word
Insurance in 2026 is becoming a clearer test of governance quality, cyber maturity, and operational resilience. Providers that can evidence leadership oversight, practical controls, tested response capability, and workforce awareness are placing themselves in a stronger position both at renewal and in day-to-day service delivery. In a year defined by tighter margins and rising expectations, cyber resilience is no longer just about reducing technical risk — it is about protecting continuity, strengthening credibility, and building a more resilient organisation overall.
Important FCA Note
This article is for general information and discussion only. It does not constitute insurance advice or a recommendation for any specific policy, broker, or insurer.
Insurance is a regulated activity under the Financial Conduct Authority. Care providers should always seek guidance from a suitably qualified and authorised insurance broker or adviser who can assess their individual circumstances and review policy wording, exclusions, and conditions in detail.